I've posted previously on the "IT/IS Skills Gap". As I'm previously noted, I'm not convinced it's necessarily due to a lack of skilled people, but in how some companies are handling filling positions.
A recent article at CSO magazine is interesting.
Friday, November 14, 2014
Wednesday, November 12, 2014
ISACA's 2014 IT Risk/Reward Barometer
Tuesday, November 11, 2014
20 Books: Daemon (2006) and Freedom™ (2010), Daniel Suarez
This is part of a sub-series of postings based on the "20 Books Cybersecurity Professionals Should Read Now".
This time I look at a couple of novels by Daniel Suarez, Daemon (2006) and its sequel Freedom™ (2010). I am a fan of "techno thrillers", and these qualify. Unlike many techno thrillers, the author knows his techno. That part is very realistic, but is a little fanciful as well. And the books are fast moving.
The books tie closely together, so I would recommend having both on hand. The plot of Daemon centers around a distributed computer program, or daemon, created by a now dead, but brilliant, game programmer. He created this program to push society in a new direction, and not in a nice way. The program recruits people to do its bidding. And it not always nice things, either. Think of the movie Eagle Eye, but taken to an extreme. For the cybersecurity professional, it's seeing how the program is able to infiltrate systems and control them to its own ends that is the most interesting. One character is even framed for a crime based on evidence planted by the program going back several months.
Like many techno thrillers, we are introduced to an array of characters on both sides of the story, good and bad. But they don't all come into the picture from the beginning, and not all of them come out at the end.
Now, I do have to say I don't agree with some of the underlying ideas the author presents as to the reason for this Daemon. His view of people and civilization doesn't match mine. I don't buy into the ideas of Naomi Klein.
This time I look at a couple of novels by Daniel Suarez, Daemon (2006) and its sequel Freedom™ (2010). I am a fan of "techno thrillers", and these qualify. Unlike many techno thrillers, the author knows his techno. That part is very realistic, but is a little fanciful as well. And the books are fast moving.
The books tie closely together, so I would recommend having both on hand. The plot of Daemon centers around a distributed computer program, or daemon, created by a now dead, but brilliant, game programmer. He created this program to push society in a new direction, and not in a nice way. The program recruits people to do its bidding. And it not always nice things, either. Think of the movie Eagle Eye, but taken to an extreme. For the cybersecurity professional, it's seeing how the program is able to infiltrate systems and control them to its own ends that is the most interesting. One character is even framed for a crime based on evidence planted by the program going back several months.
Like many techno thrillers, we are introduced to an array of characters on both sides of the story, good and bad. But they don't all come into the picture from the beginning, and not all of them come out at the end.
Now, I do have to say I don't agree with some of the underlying ideas the author presents as to the reason for this Daemon. His view of people and civilization doesn't match mine. I don't buy into the ideas of Naomi Klein.
Monday, November 10, 2014
Is the Information Security Skills Gap misidentified?
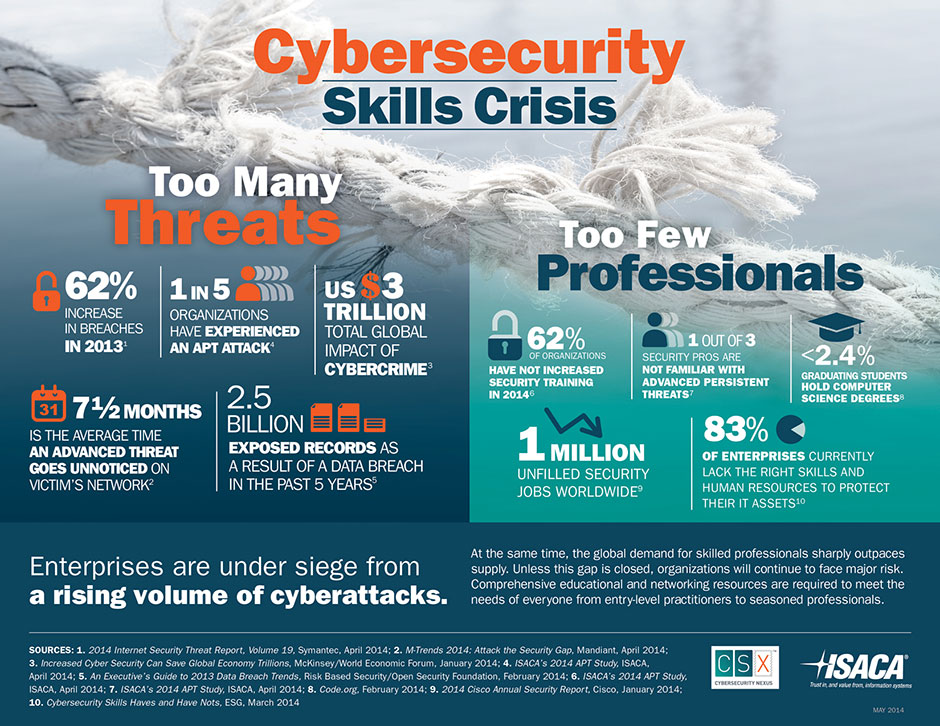
In recent postings, I've touched on the information security skills gap. Many individuals and groups are pushing the idea that the large number of unfilled information security positions (40% is a number I've seen tossed around) is due to a "skills gap", that there are not enough skilled individuals to fill them. And so we need to pump out more infosec professionals.
As noted, I'm not in agreement with this idea. There may be a skills gap in certain areas and in certain markets, but don't think its correct to say we have an overall skills gap.
As noted, I'm not in agreement with this idea. There may be a skills gap in certain areas and in certain markets, but don't think its correct to say we have an overall skills gap.
Thursday, November 6, 2014
ISSA's Cybersecurity Career Lifecycle
At the recent ISSA International Conference in Orlando, they rolled out a new program, the Cybersecurity Career Lifecycle (CSCL).
The CSCL is meant to be an industry-wide initiative to bring a level of professionalism. It defines and maps the five stages of the cybersecurity career lifecycle. For each of these stages, the framework defines the knowledge, skills, aptitudes and responsibilities, thereby allowing cybersecurity professionals to identify the current stage of their career.
The first stages are:
Article on it at Security Week.
The CSCL is meant to be an industry-wide initiative to bring a level of professionalism. It defines and maps the five stages of the cybersecurity career lifecycle. For each of these stages, the framework defines the knowledge, skills, aptitudes and responsibilities, thereby allowing cybersecurity professionals to identify the current stage of their career.
The first stages are:
- pre-professional (students, young adults),
- entry level (1-2 years)
- mid-career (3-7 years)
- senior level (7+ years)
- executive level (12+ years)
More is coming, and this looks very interesting.
Article on it at Security Week.
Wednesday, November 5, 2014
Security and Android Lollipop
By now people have heard that the next version of Android, up to now being called "L" has a name and version number: 5.0 Lollipop. It should be going out now to Nexus devices, no idea the schedule for others.
And with any new version of Android, we have to wonder about the security features of it. Over the last few versions, we've seen Google make Android more secure and more "enterprise ready". The biggest part of this was integration of some of Samsung's Knox product. (which is kind of disappointing, as Google had the opportunity to integrate 3LM's work, which came from former Google engineers).
And with any new version of Android, we have to wonder about the security features of it. Over the last few versions, we've seen Google make Android more secure and more "enterprise ready". The biggest part of this was integration of some of Samsung's Knox product. (which is kind of disappointing, as Google had the opportunity to integrate 3LM's work, which came from former Google engineers).
Tuesday, November 4, 2014
Is there an IT Security Skill Set Gap??
Over the last year or so, I have heard from several sources that we have a "cybersecurity skills gap". That we have more IT security positions then we have skilled people to fill them.
Here is one example of such claims:
Now, as an experienced cybersecurity professional who has been on the job market for some time without too much success, I have a hard time accepting this. Why do I say this?
Here is one example of such claims:
Now, as an experienced cybersecurity professional who has been on the job market for some time without too much success, I have a hard time accepting this. Why do I say this?
Monday, November 3, 2014
20 Books: Zero Day (2011) and Trojan Horse (2012), Mark Russinovich
This is part of a sub-series of postings based on the "20 Books Cybersecurity Professionals Should Read Now".
This time we have another pair of novels, Zero Day (2011) and Trojan Horse (2012) by Mark Russinovich. Russinovich cofounded Winternals, and is now a Technical Fellow at Microsoft. These techno thrillers star Jeff Aiken, a former government analyst. These are more cerebral thrillers, then action thrillers. Aiken is not an action hero.
But these works are very grounded in real world security issues, as well as political matters.
The main character is Jeff Aiken, who we meet in the first work. He is a cybersecurity expert. He used to work for the CIA, but left after he had submitted a report that predicted 9/11 that his boss, unknown to him, squashed the report. He warned his fiance to stay away from the World Trade Center that day, but she went with a friend and was killed. He has since formed his own consulting firm, working for both private and government groups. We also meet a fellow expert, Daryl Haugen, who is working for the NSA in the first work, and leaves the NSA to join him in his firm at the end of that work.
Zero Day is built around the idea of a "zero day exploit", an unknown exploit that is taken advantage of before companies can get a patch out. Here, Muslim jihadist are working to take advantage of such exploits in code put together by various hackers, and distributed by third parties who don't know what they are really doing. They hope to cause a massive collapse of Western systems, but Aiken is alerted to the issue when he is brought in to fix a system that was affected by the infected systems too soon. Aiken and Haugen are quickly on the trail, in hopes of stopping things before they get out of hand.
Trojan Horse also makes use of computer exploits, but also gets into state-supported hacking, when nation-states make use of hacking against other nations for their advantage. The Stuxnet virus is claimed to be such a real world example of this. Here, we have Iran working to build a nuclear weapon, with China using their military hackers to help them out, but working to keep that hidden. Again, Aiken and Haugen are asked to look at an unusual computer incident, which soon puts them on the trail of the hackers.
Since these 2 novels came out, there is now a short story available on the Kindle, "Operation Desolation" and a new novel, Rogue Code, has just come out this past month. Am hoping when Rogue Code is released in paperback, they include the short story. (seen this done with similar works by other authors).
Check out these works. I like techno-thrillers, and I found these to be fairly well grounded in today's world, both technically and politically.
But these works are very grounded in real world security issues, as well as political matters.
The main character is Jeff Aiken, who we meet in the first work. He is a cybersecurity expert. He used to work for the CIA, but left after he had submitted a report that predicted 9/11 that his boss, unknown to him, squashed the report. He warned his fiance to stay away from the World Trade Center that day, but she went with a friend and was killed. He has since formed his own consulting firm, working for both private and government groups. We also meet a fellow expert, Daryl Haugen, who is working for the NSA in the first work, and leaves the NSA to join him in his firm at the end of that work.
Zero Day is built around the idea of a "zero day exploit", an unknown exploit that is taken advantage of before companies can get a patch out. Here, Muslim jihadist are working to take advantage of such exploits in code put together by various hackers, and distributed by third parties who don't know what they are really doing. They hope to cause a massive collapse of Western systems, but Aiken is alerted to the issue when he is brought in to fix a system that was affected by the infected systems too soon. Aiken and Haugen are quickly on the trail, in hopes of stopping things before they get out of hand.
Trojan Horse also makes use of computer exploits, but also gets into state-supported hacking, when nation-states make use of hacking against other nations for their advantage. The Stuxnet virus is claimed to be such a real world example of this. Here, we have Iran working to build a nuclear weapon, with China using their military hackers to help them out, but working to keep that hidden. Again, Aiken and Haugen are asked to look at an unusual computer incident, which soon puts them on the trail of the hackers.
Since these 2 novels came out, there is now a short story available on the Kindle, "Operation Desolation" and a new novel, Rogue Code, has just come out this past month. Am hoping when Rogue Code is released in paperback, they include the short story. (seen this done with similar works by other authors).
Check out these works. I like techno-thrillers, and I found these to be fairly well grounded in today's world, both technically and politically.
Subscribe to:
Comments (Atom)