I've posted previously on the "IT/IS Skills Gap". As I'm previously noted, I'm not convinced it's necessarily due to a lack of skilled people, but in how some companies are handling filling positions.
A recent article at CSO magazine is interesting.
Friday, November 14, 2014
Wednesday, November 12, 2014
ISACA's 2014 IT Risk/Reward Barometer
Tuesday, November 11, 2014
20 Books: Daemon (2006) and Freedom™ (2010), Daniel Suarez
This is part of a sub-series of postings based on the "20 Books Cybersecurity Professionals Should Read Now".
This time I look at a couple of novels by Daniel Suarez, Daemon (2006) and its sequel Freedom™ (2010). I am a fan of "techno thrillers", and these qualify. Unlike many techno thrillers, the author knows his techno. That part is very realistic, but is a little fanciful as well. And the books are fast moving.
The books tie closely together, so I would recommend having both on hand. The plot of Daemon centers around a distributed computer program, or daemon, created by a now dead, but brilliant, game programmer. He created this program to push society in a new direction, and not in a nice way. The program recruits people to do its bidding. And it not always nice things, either. Think of the movie Eagle Eye, but taken to an extreme. For the cybersecurity professional, it's seeing how the program is able to infiltrate systems and control them to its own ends that is the most interesting. One character is even framed for a crime based on evidence planted by the program going back several months.
Like many techno thrillers, we are introduced to an array of characters on both sides of the story, good and bad. But they don't all come into the picture from the beginning, and not all of them come out at the end.
Now, I do have to say I don't agree with some of the underlying ideas the author presents as to the reason for this Daemon. His view of people and civilization doesn't match mine. I don't buy into the ideas of Naomi Klein.
This time I look at a couple of novels by Daniel Suarez, Daemon (2006) and its sequel Freedom™ (2010). I am a fan of "techno thrillers", and these qualify. Unlike many techno thrillers, the author knows his techno. That part is very realistic, but is a little fanciful as well. And the books are fast moving.
The books tie closely together, so I would recommend having both on hand. The plot of Daemon centers around a distributed computer program, or daemon, created by a now dead, but brilliant, game programmer. He created this program to push society in a new direction, and not in a nice way. The program recruits people to do its bidding. And it not always nice things, either. Think of the movie Eagle Eye, but taken to an extreme. For the cybersecurity professional, it's seeing how the program is able to infiltrate systems and control them to its own ends that is the most interesting. One character is even framed for a crime based on evidence planted by the program going back several months.
Like many techno thrillers, we are introduced to an array of characters on both sides of the story, good and bad. But they don't all come into the picture from the beginning, and not all of them come out at the end.
Now, I do have to say I don't agree with some of the underlying ideas the author presents as to the reason for this Daemon. His view of people and civilization doesn't match mine. I don't buy into the ideas of Naomi Klein.
Monday, November 10, 2014
Is the Information Security Skills Gap misidentified?
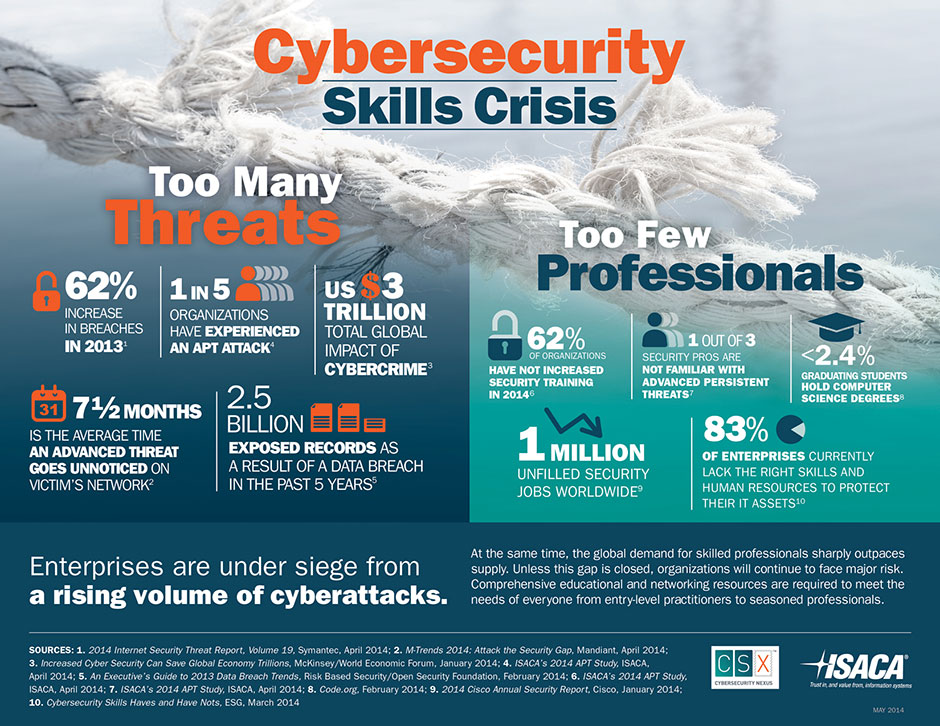
In recent postings, I've touched on the information security skills gap. Many individuals and groups are pushing the idea that the large number of unfilled information security positions (40% is a number I've seen tossed around) is due to a "skills gap", that there are not enough skilled individuals to fill them. And so we need to pump out more infosec professionals.
As noted, I'm not in agreement with this idea. There may be a skills gap in certain areas and in certain markets, but don't think its correct to say we have an overall skills gap.
As noted, I'm not in agreement with this idea. There may be a skills gap in certain areas and in certain markets, but don't think its correct to say we have an overall skills gap.
Thursday, November 6, 2014
ISSA's Cybersecurity Career Lifecycle
At the recent ISSA International Conference in Orlando, they rolled out a new program, the Cybersecurity Career Lifecycle (CSCL).
The CSCL is meant to be an industry-wide initiative to bring a level of professionalism. It defines and maps the five stages of the cybersecurity career lifecycle. For each of these stages, the framework defines the knowledge, skills, aptitudes and responsibilities, thereby allowing cybersecurity professionals to identify the current stage of their career.
The first stages are:
Article on it at Security Week.
The CSCL is meant to be an industry-wide initiative to bring a level of professionalism. It defines and maps the five stages of the cybersecurity career lifecycle. For each of these stages, the framework defines the knowledge, skills, aptitudes and responsibilities, thereby allowing cybersecurity professionals to identify the current stage of their career.
The first stages are:
- pre-professional (students, young adults),
- entry level (1-2 years)
- mid-career (3-7 years)
- senior level (7+ years)
- executive level (12+ years)
More is coming, and this looks very interesting.
Article on it at Security Week.
Wednesday, November 5, 2014
Security and Android Lollipop
By now people have heard that the next version of Android, up to now being called "L" has a name and version number: 5.0 Lollipop. It should be going out now to Nexus devices, no idea the schedule for others.
And with any new version of Android, we have to wonder about the security features of it. Over the last few versions, we've seen Google make Android more secure and more "enterprise ready". The biggest part of this was integration of some of Samsung's Knox product. (which is kind of disappointing, as Google had the opportunity to integrate 3LM's work, which came from former Google engineers).
And with any new version of Android, we have to wonder about the security features of it. Over the last few versions, we've seen Google make Android more secure and more "enterprise ready". The biggest part of this was integration of some of Samsung's Knox product. (which is kind of disappointing, as Google had the opportunity to integrate 3LM's work, which came from former Google engineers).
Tuesday, November 4, 2014
Is there an IT Security Skill Set Gap??
Over the last year or so, I have heard from several sources that we have a "cybersecurity skills gap". That we have more IT security positions then we have skilled people to fill them.
Here is one example of such claims:
Now, as an experienced cybersecurity professional who has been on the job market for some time without too much success, I have a hard time accepting this. Why do I say this?
Here is one example of such claims:
Now, as an experienced cybersecurity professional who has been on the job market for some time without too much success, I have a hard time accepting this. Why do I say this?
Monday, November 3, 2014
20 Books: Zero Day (2011) and Trojan Horse (2012), Mark Russinovich
This is part of a sub-series of postings based on the "20 Books Cybersecurity Professionals Should Read Now".
This time we have another pair of novels, Zero Day (2011) and Trojan Horse (2012) by Mark Russinovich. Russinovich cofounded Winternals, and is now a Technical Fellow at Microsoft. These techno thrillers star Jeff Aiken, a former government analyst. These are more cerebral thrillers, then action thrillers. Aiken is not an action hero.
But these works are very grounded in real world security issues, as well as political matters.
The main character is Jeff Aiken, who we meet in the first work. He is a cybersecurity expert. He used to work for the CIA, but left after he had submitted a report that predicted 9/11 that his boss, unknown to him, squashed the report. He warned his fiance to stay away from the World Trade Center that day, but she went with a friend and was killed. He has since formed his own consulting firm, working for both private and government groups. We also meet a fellow expert, Daryl Haugen, who is working for the NSA in the first work, and leaves the NSA to join him in his firm at the end of that work.
Zero Day is built around the idea of a "zero day exploit", an unknown exploit that is taken advantage of before companies can get a patch out. Here, Muslim jihadist are working to take advantage of such exploits in code put together by various hackers, and distributed by third parties who don't know what they are really doing. They hope to cause a massive collapse of Western systems, but Aiken is alerted to the issue when he is brought in to fix a system that was affected by the infected systems too soon. Aiken and Haugen are quickly on the trail, in hopes of stopping things before they get out of hand.
Trojan Horse also makes use of computer exploits, but also gets into state-supported hacking, when nation-states make use of hacking against other nations for their advantage. The Stuxnet virus is claimed to be such a real world example of this. Here, we have Iran working to build a nuclear weapon, with China using their military hackers to help them out, but working to keep that hidden. Again, Aiken and Haugen are asked to look at an unusual computer incident, which soon puts them on the trail of the hackers.
Since these 2 novels came out, there is now a short story available on the Kindle, "Operation Desolation" and a new novel, Rogue Code, has just come out this past month. Am hoping when Rogue Code is released in paperback, they include the short story. (seen this done with similar works by other authors).
Check out these works. I like techno-thrillers, and I found these to be fairly well grounded in today's world, both technically and politically.
But these works are very grounded in real world security issues, as well as political matters.
The main character is Jeff Aiken, who we meet in the first work. He is a cybersecurity expert. He used to work for the CIA, but left after he had submitted a report that predicted 9/11 that his boss, unknown to him, squashed the report. He warned his fiance to stay away from the World Trade Center that day, but she went with a friend and was killed. He has since formed his own consulting firm, working for both private and government groups. We also meet a fellow expert, Daryl Haugen, who is working for the NSA in the first work, and leaves the NSA to join him in his firm at the end of that work.
Zero Day is built around the idea of a "zero day exploit", an unknown exploit that is taken advantage of before companies can get a patch out. Here, Muslim jihadist are working to take advantage of such exploits in code put together by various hackers, and distributed by third parties who don't know what they are really doing. They hope to cause a massive collapse of Western systems, but Aiken is alerted to the issue when he is brought in to fix a system that was affected by the infected systems too soon. Aiken and Haugen are quickly on the trail, in hopes of stopping things before they get out of hand.
Trojan Horse also makes use of computer exploits, but also gets into state-supported hacking, when nation-states make use of hacking against other nations for their advantage. The Stuxnet virus is claimed to be such a real world example of this. Here, we have Iran working to build a nuclear weapon, with China using their military hackers to help them out, but working to keep that hidden. Again, Aiken and Haugen are asked to look at an unusual computer incident, which soon puts them on the trail of the hackers.
Since these 2 novels came out, there is now a short story available on the Kindle, "Operation Desolation" and a new novel, Rogue Code, has just come out this past month. Am hoping when Rogue Code is released in paperback, they include the short story. (seen this done with similar works by other authors).
Check out these works. I like techno-thrillers, and I found these to be fairly well grounded in today's world, both technically and politically.
Monday, October 13, 2014
2014 ISSA International Conference
On October 22-23 in Orlando, ISSA (International System Security Association) is holding their 2014 International Conference. I am attending, and this will be my first time at this event. Also, as I'm the Secretary of our local chapter, am going to be up there on the 21st for the Chapter Leader's Summit.
I plan to report here on my impressions of the event.
Hope I see some of you there.
I plan to report here on my impressions of the event.
Hope I see some of you there.
Friday, October 10, 2014
ITpalooza 2014
Here in my local area, we have an event aimed at IT people during the holidays called ITpalooza. Now in it's third year, this event aims to bring together the various user groups and professional associations, along with vendors and recruiters, and have various speakers.
ITpalooza 2014 will be held December 4th at Nova Southeastern University. It runs all day, with speakers, training, fun stuff and more.
Check out the website. The event is FREE.
ITpalooza 2014 will be held December 4th at Nova Southeastern University. It runs all day, with speakers, training, fun stuff and more.
Check out the website. The event is FREE.
Thursday, October 9, 2014
ISACA's new Cybersecurity Nexus
ISACA, the professional association for those involved in IT Audit and Controls, has decided to move into the realm of "cybersecurity" with their Cybersecurity Nexus (CSX).
I've been a member off and on for several years, but for me the group was about IT audits and IT control, such as COBIT. I joined other organizations for cybersecurity, such as ISSA, and SANS. I don't know why ISACA feels they need to move into that area, it's not like there is a need for yet another group involved here.
Further, as part of this, they've created a new entry level certificate, Cybersecurity Fundamentals. This is meant for those just getting into cybersecurity. It has no experience requirements, nor does it expire. For me, certificates that don't require experience or don't expire are not as valuable as those which do. And unlike ISACA's other certifications, this one is taken on-line on-demand.
I'm one of those people who doesn't see the value in duplicating effort. I feel they are duplicating effort that is already being done by other organizations (ISSA, ISC(2), SANS, etc). I'd rather see them partner with an existing group then move beyond their "core purpose".
Any other thoughts?
I've been a member off and on for several years, but for me the group was about IT audits and IT control, such as COBIT. I joined other organizations for cybersecurity, such as ISSA, and SANS. I don't know why ISACA feels they need to move into that area, it's not like there is a need for yet another group involved here.
Further, as part of this, they've created a new entry level certificate, Cybersecurity Fundamentals. This is meant for those just getting into cybersecurity. It has no experience requirements, nor does it expire. For me, certificates that don't require experience or don't expire are not as valuable as those which do. And unlike ISACA's other certifications, this one is taken on-line on-demand.
I'm one of those people who doesn't see the value in duplicating effort. I feel they are duplicating effort that is already being done by other organizations (ISSA, ISC(2), SANS, etc). I'd rather see them partner with an existing group then move beyond their "core purpose".
Any other thoughts?
Wednesday, October 8, 2014
October is National Cyber Security Awareness Month 2014
For those not aware, October is National Cyber Security Awareness Month.
"NCSAM is designed to engage and educate public and private sector partners through events and initiatives with the goal of raising awareness about cybersecurity and increasing the resiliency of the nation in the event of a cyber incident. October 2014 marks the 11th annual National Cyber Security Awareness Month sponsored by the Department of Homeland Security in cooperation with the National Cyber Security Alliance (NCSA) and the Multi-State Information Sharing and Analysis Center (MS-ISAC)."
Now, locally, Nova Southeastern University's Graduate School of Computer and Information Sciences is hosting a series of events that tie in with NSCAM.
Among their public events are:
* September 30- FBI Special Presentation on "Cyber Security Threats and Trends"
* October 22- DHS Special Presentation on Cybersecurity: A Shared Responsibility
In addition, they have had other events for selected groups, like high school students and college students.
What is happening locally for you??
"NCSAM is designed to engage and educate public and private sector partners through events and initiatives with the goal of raising awareness about cybersecurity and increasing the resiliency of the nation in the event of a cyber incident. October 2014 marks the 11th annual National Cyber Security Awareness Month sponsored by the Department of Homeland Security in cooperation with the National Cyber Security Alliance (NCSA) and the Multi-State Information Sharing and Analysis Center (MS-ISAC)."
Now, locally, Nova Southeastern University's Graduate School of Computer and Information Sciences is hosting a series of events that tie in with NSCAM.
Among their public events are:
* September 30- FBI Special Presentation on "Cyber Security Threats and Trends"
* October 22- DHS Special Presentation on Cybersecurity: A Shared Responsibility
In addition, they have had other events for selected groups, like high school students and college students.
What is happening locally for you??
I'm back!
After too long, am back to posting new items to my blog.
There are several items I am working on. Here are some:
* further postings on the 20 books.
* Android security
* Security frameworks, such as NIST Cybersecurity Framework
* recent breaches
* the security skillset issue
* upcoming events
and more
There are several items I am working on. Here are some:
* further postings on the 20 books.
* Android security
* Security frameworks, such as NIST Cybersecurity Framework
* recent breaches
* the security skillset issue
* upcoming events
and more
Wednesday, May 7, 2014
20 Books: Cryptonomicon
This is part of a sub-series of postings based on the "20 Books Cybersecurity Professionals Should Read Now".
Neil Stephenson is one of the leading authors in the "cyberpunk" genre, which I covered in a prior posting about Neuromancer. Not surprisingly, he has 3 of his works on this list. I already covered his earlier work, Snow Crash (1992). Now I move to what is considered his second masterpiece, Cryptonomicon.
In this work, there are two separate, but connected storylines. The storylines are separated by time, but have some of the same characters or linked between the two groups.
One storyline is set during WWII and centered around Lawrence Pritchard Waterhouse, a young United States Navy code breaker and mathematical genius. He is assigned to the newly formed group called Detachment 2702. Their focus is to keep the Axis from knowing that the Allies has broken the Enigma code.
The second storyline is set in the 1990s, and centers around Randy Waterhouse (Lawrence's grandson). He involved in a venture with others that involved creating a secure data haven and cryptography.
The book gets into some cryptographic details, which may be off putting for some people.
I do recall after reading it at the time that I figured there would be a sequel, but instead he wrote a prequel trilogy called the Baroque Cycle.
Neil Stephenson is one of the leading authors in the "cyberpunk" genre, which I covered in a prior posting about Neuromancer. Not surprisingly, he has 3 of his works on this list. I already covered his earlier work, Snow Crash (1992). Now I move to what is considered his second masterpiece, Cryptonomicon.
In this work, there are two separate, but connected storylines. The storylines are separated by time, but have some of the same characters or linked between the two groups.
One storyline is set during WWII and centered around Lawrence Pritchard Waterhouse, a young United States Navy code breaker and mathematical genius. He is assigned to the newly formed group called Detachment 2702. Their focus is to keep the Axis from knowing that the Allies has broken the Enigma code.
The second storyline is set in the 1990s, and centers around Randy Waterhouse (Lawrence's grandson). He involved in a venture with others that involved creating a secure data haven and cryptography.
The book gets into some cryptographic details, which may be off putting for some people.
I do recall after reading it at the time that I figured there would be a sequel, but instead he wrote a prequel trilogy called the Baroque Cycle.
Thursday, May 1, 2014
20 Books: Snow Crash
This is part of a sub-series of postings based on the "20 Books Cybersecurity Professionals Should Read Now".
Neil Stephenson is one of the leading authors in the "cyberpunk" genre, which I covered in a prior posting about Neuromancer. Not surprisingly, he has 3 of his works on this list. Snow Crash (1992) is the earliest of the three, so figured we'd start with this one.
Set in the near future where the United States (and probably the world) has broken down into a large number of sovereign enclaves. Most everything is privatized, including roads and mail service. The internet (cyberspace) is known as the Metaverse.
A new virus has been released which is both a computer virus and a neurological virus. The nominal heroes of the story, hacker Hiro Protaganist and Y.T., must work to figure out the mystery behind the Snow Crash virus before its too late.
While that seems fairly straight forward, Stephenson's works include a LOT of other concepts. We get ideas about language being a virus, and that our development of multiple languages was a defense from having a single language and its vulnerabilities.
Some of the concepts in the book actually inspired real systems, such as Google Earth.
Because of the interesting ideas in his works, I recommend checking Stephenson out.
Neil Stephenson is one of the leading authors in the "cyberpunk" genre, which I covered in a prior posting about Neuromancer. Not surprisingly, he has 3 of his works on this list. Snow Crash (1992) is the earliest of the three, so figured we'd start with this one.
Set in the near future where the United States (and probably the world) has broken down into a large number of sovereign enclaves. Most everything is privatized, including roads and mail service. The internet (cyberspace) is known as the Metaverse.
A new virus has been released which is both a computer virus and a neurological virus. The nominal heroes of the story, hacker Hiro Protaganist and Y.T., must work to figure out the mystery behind the Snow Crash virus before its too late.
While that seems fairly straight forward, Stephenson's works include a LOT of other concepts. We get ideas about language being a virus, and that our development of multiple languages was a defense from having a single language and its vulnerabilities.
Some of the concepts in the book actually inspired real systems, such as Google Earth.
Because of the interesting ideas in his works, I recommend checking Stephenson out.
Wednesday, April 23, 2014
Currently Reading: Schneier on Security
A book that I am currently reading is Schneier on Security (2008) by Bruce Schneier.
I would hope that most security professionals out there are familiar with Bruce. He has written several books and numerous articles. His blog, Schneier on Security, is well known as is his monthly e-newsletter Crypto-Gram (go to his blog to read and subscribe).
For myself, I've read many of his materials and seldom disagree with his views. I think mainly where I think he may not have all the info, I disagree with his conclusions. Frankly, I find that too many other security experts of his caliber are sadly a bit stuck in their ways and the views are too off.
Schneier is known for actually criticizing many of the so-called "security" measures put into place for really failing to make us more secure. He called this "security theater". So while some so-called experts push for new IDs or more surveillance, Schneier points out that all this stuff doesn't do what it claims, and may, in fact, make us less secure. You have to wonder what the real reason some people push these methods?
Schneier on Security is a collection of essays written between 2002 and 2008 that have appeared in various magazines, newspapers, websites and Crypto-Gram. A few he updated at the time of the publication of the book (2008), and all cite the original publication. Sadly, being over 5 years old, some of the statements are now a little dated, but if you overlook that, there are many interesting items here.
The book is organized into a dozen chapters:
<updated 5/1/2014>
I would hope that most security professionals out there are familiar with Bruce. He has written several books and numerous articles. His blog, Schneier on Security, is well known as is his monthly e-newsletter Crypto-Gram (go to his blog to read and subscribe).
For myself, I've read many of his materials and seldom disagree with his views. I think mainly where I think he may not have all the info, I disagree with his conclusions. Frankly, I find that too many other security experts of his caliber are sadly a bit stuck in their ways and the views are too off.
Schneier is known for actually criticizing many of the so-called "security" measures put into place for really failing to make us more secure. He called this "security theater". So while some so-called experts push for new IDs or more surveillance, Schneier points out that all this stuff doesn't do what it claims, and may, in fact, make us less secure. You have to wonder what the real reason some people push these methods?
Schneier on Security is a collection of essays written between 2002 and 2008 that have appeared in various magazines, newspapers, websites and Crypto-Gram. A few he updated at the time of the publication of the book (2008), and all cite the original publication. Sadly, being over 5 years old, some of the statements are now a little dated, but if you overlook that, there are many interesting items here.
The book is organized into a dozen chapters:
- Terrorism and Security
- National Security Policy
- Airline Travel
- Privacy and Surveillance
- ID Cards and Security
- Election Security
- Security and Disasters
- Economics of Security
- Psychology of Security
- Business of Security
- Cybercrime and Cyberwar
- Computer and Information Security
Because each essay is fairly short (2-3 pages max), and most are just gathered into each chapter by common topic, one can jump around and read what sparks your interest. In fact, that's what I have been doing.
As some of the topics go beyond just technical information security that many of us in the infosec world focus on, I think its good that we have a better understanding of security outside of IT, as well as the impact of what we do affects other areas.
So check it out. And if you like what you see, check out his other works as well. His latest book, Carry On, is actually a "sequel" to this work, collecting articles from 2008-2013. I don't have it yet, but plan on getting it soon.
<updated 5/1/2014>
Sunday, April 13, 2014
20 Books: Neuromancer
This is part of a sub-series of postings based on the "20 Books Cybersecurity Professionals Should Read Now".
William Gibson's Neuromancer (1984) is considered one of the seminal works of cyberpunk. Ok, so what is "cyberpunk"? Its a genre of science-fiction that is set in the near-future. It shows a world that has both high tech, such as advanced information technology and cybernetics, but also shows a degree of breakdown of the social order. Some could even be a bit dystopic. Cyberpunk would spawn other genres. Attempts to push the ideas of cyberpunk into prior technology periods would result in "steampunk" and "dieselpunk" genres. And other genres would be spawned that would be thispunk and thatpunk that got tiresome.
Why we as info sec professionals should care is that in much of the cyberpunk genre, cyberspace, the world on-line, usually has a big place in the stories. And as such, hacking and security and all that will have a big part to play.
Gibson is considered one of the main originators of the genre, and Neuromancer was his first novel, and the first in his "Sprawl" series. I read it and other cyberpunk works soon after they came out. As a young computer science major in college, I recall trying to grasp the world being explained. Keep in mind that at the time the Internet was not available to many people. The idea of cyberspace was then pure science fiction. We didn't have the Internet, WWW, and all the rest to reference to.
As one of the first cyberpunk works, it sets the stage for others, so I think its important to be familiar with it, and the world of hackers and the computer underground it shows. If you haven't already read it, check it out.
I should point out that the Keanu Reaves movie, Johnny Mneumonic is loosely based on a short story of the same name that precedes Neuromancer, But the movie doesn't quite match up with the story. Big surprise.
William Gibson's Neuromancer (1984) is considered one of the seminal works of cyberpunk. Ok, so what is "cyberpunk"? Its a genre of science-fiction that is set in the near-future. It shows a world that has both high tech, such as advanced information technology and cybernetics, but also shows a degree of breakdown of the social order. Some could even be a bit dystopic. Cyberpunk would spawn other genres. Attempts to push the ideas of cyberpunk into prior technology periods would result in "steampunk" and "dieselpunk" genres. And other genres would be spawned that would be thispunk and thatpunk that got tiresome.
Why we as info sec professionals should care is that in much of the cyberpunk genre, cyberspace, the world on-line, usually has a big place in the stories. And as such, hacking and security and all that will have a big part to play.
Gibson is considered one of the main originators of the genre, and Neuromancer was his first novel, and the first in his "Sprawl" series. I read it and other cyberpunk works soon after they came out. As a young computer science major in college, I recall trying to grasp the world being explained. Keep in mind that at the time the Internet was not available to many people. The idea of cyberspace was then pure science fiction. We didn't have the Internet, WWW, and all the rest to reference to.
As one of the first cyberpunk works, it sets the stage for others, so I think its important to be familiar with it, and the world of hackers and the computer underground it shows. If you haven't already read it, check it out.
I should point out that the Keanu Reaves movie, Johnny Mneumonic is loosely based on a short story of the same name that precedes Neuromancer, But the movie doesn't quite match up with the story. Big surprise.
Thursday, April 10, 2014
20 Books: Cuckoo's Egg
This is part of a sub-series of postings based on the "20 Books Cybersecurity Professionals Should Read Now".
Clifford's Stoll's book, The Cuckoo's Egg (or to use it's full title The Cuckoo's Egg: Tracking a Spy Through the Maze of Computer Espionage) is an early (1989) work on computer breaches and espionage. I read it when it first came out, and I thought it fascinating at the time.
For those not aware, let's get into it.
Clifford Stoll was at the time (1986) an unemployed astronomer working as a Unix sysadmin at the Lawrence Berkeley National Laboratory. His boss asked him to looking to a 75cents error in computer usage. Back in those days, you would be charged for computer usage.
Now, the amount was strange. An anomaly. That is important. Otherwise why bother? It's a trivial amount. Some companies would just write off a bill of that size as not worth their time. But this is what triggered things, as it indicated that it wasn't a system error, but a human error. Someone was hiding (or trying to hide) their tracks. And this mistake lead to the anomaly, which lead to Stoll looking into it.
Keep in mind this was way before the various cybersecurity systems we think of existed. No firewalls. No IDS/IPS or the like. This was because access was being done in many cases over modems, NOT the Internet. From his 10 month investigation, Stoll realized this was bigger then just a simple accounting error, and soon brought in the authorities. Its also interesting that Stoll's girlfriend actually recommended he setup what today would be known as a "honeypot" to attract the hackers and keep them on-line so they could be traced.
It developed that the hackers were from Germany. It also seemed they'd accessed LBL by mistake, thinking it was Lawrence Livermore National Laboratory, where they do nuclear research. Thanks to Stoll's efforts, the hacker and a confederate were captured and put on trial. It would later be shown that the hackers (or some of them) were doing espionage for the KGB.
Stoll wrote up the matter in a more technical article for the Association of Computing Machinery (ACM) called "Stalking the Wiley Hacker" in 1988. You can read this
The book came next, written for the general audience.
And they then did an episode of the PBS science series NOVA on it: "The KGB, The Computer, and Me" in 1990. Interestingly, many of the people involved played themselves.
While the technology may seem primitive, it shows how small, anomalous things can point to bigger issues. Clearly, you don't want to have to spend 10 months tracking down the source of a computer breach, but having an idea of what is normal on your systems such that abnormal things, no matter how small, can point to bigger issues.
All these works are highly recommended by me. Check them out!
Clifford's Stoll's book, The Cuckoo's Egg (or to use it's full title The Cuckoo's Egg: Tracking a Spy Through the Maze of Computer Espionage) is an early (1989) work on computer breaches and espionage. I read it when it first came out, and I thought it fascinating at the time.
For those not aware, let's get into it.
Clifford Stoll was at the time (1986) an unemployed astronomer working as a Unix sysadmin at the Lawrence Berkeley National Laboratory. His boss asked him to looking to a 75cents error in computer usage. Back in those days, you would be charged for computer usage.
Now, the amount was strange. An anomaly. That is important. Otherwise why bother? It's a trivial amount. Some companies would just write off a bill of that size as not worth their time. But this is what triggered things, as it indicated that it wasn't a system error, but a human error. Someone was hiding (or trying to hide) their tracks. And this mistake lead to the anomaly, which lead to Stoll looking into it.
Keep in mind this was way before the various cybersecurity systems we think of existed. No firewalls. No IDS/IPS or the like. This was because access was being done in many cases over modems, NOT the Internet. From his 10 month investigation, Stoll realized this was bigger then just a simple accounting error, and soon brought in the authorities. Its also interesting that Stoll's girlfriend actually recommended he setup what today would be known as a "honeypot" to attract the hackers and keep them on-line so they could be traced.
It developed that the hackers were from Germany. It also seemed they'd accessed LBL by mistake, thinking it was Lawrence Livermore National Laboratory, where they do nuclear research. Thanks to Stoll's efforts, the hacker and a confederate were captured and put on trial. It would later be shown that the hackers (or some of them) were doing espionage for the KGB.
Stoll wrote up the matter in a more technical article for the Association of Computing Machinery (ACM) called "Stalking the Wiley Hacker" in 1988. You can read this
The book came next, written for the general audience.
And they then did an episode of the PBS science series NOVA on it: "The KGB, The Computer, and Me" in 1990. Interestingly, many of the people involved played themselves.
While the technology may seem primitive, it shows how small, anomalous things can point to bigger issues. Clearly, you don't want to have to spend 10 months tracking down the source of a computer breach, but having an idea of what is normal on your systems such that abnormal things, no matter how small, can point to bigger issues.
All these works are highly recommended by me. Check them out!
Wednesday, April 9, 2014
Security BSides Orlando 2014
This past weekend I attended the Security BSides Orlando conference. I have heard of these conferences held around the country, but it was my first time attending any.
For those not aware, Security BSides Conferences are community lead and organized conferences. They are intended to be a way for the information security community to be able to come together and share ideas in a more informal setting, often at a very low cost to the attendees. A model or framework has been set down in which people can setup their own conferences. You can read more about this HERE.
Here in Florida we have had 2 in Orlando, one in Tampa Bay, and one coming up in Jacksonville. Would love to see one in South Florida. (hint hint)
I have had experience with other security conferences (Hacker Halted, South Florida ISSA and South Florida ISACA, HackMiami). I would say it was more similar to HackMiami's conference in terms of being more low key then what I've seen with the others, but also a lot cheaper then HackMiami's.
There were 2 tracks of speakers, with another on Saturday of more class type sessions. There was also a small vendor room that had a few of the sponsors, as well as a "lockpick village" to try out lock picking, and a Maker Lab (FemiLab from central Florida) in attendance. Also in the room they had a CTF event going on as well all weekend. This was also rounded out with a party on Saturday night.
Overall, a good event. Look forward to next year's event. I hope to submit a proposal for a talk as well.
For those not aware, Security BSides Conferences are community lead and organized conferences. They are intended to be a way for the information security community to be able to come together and share ideas in a more informal setting, often at a very low cost to the attendees. A model or framework has been set down in which people can setup their own conferences. You can read more about this HERE.
Here in Florida we have had 2 in Orlando, one in Tampa Bay, and one coming up in Jacksonville. Would love to see one in South Florida. (hint hint)
I have had experience with other security conferences (Hacker Halted, South Florida ISSA and South Florida ISACA, HackMiami). I would say it was more similar to HackMiami's conference in terms of being more low key then what I've seen with the others, but also a lot cheaper then HackMiami's.
There were 2 tracks of speakers, with another on Saturday of more class type sessions. There was also a small vendor room that had a few of the sponsors, as well as a "lockpick village" to try out lock picking, and a Maker Lab (FemiLab from central Florida) in attendance. Also in the room they had a CTF event going on as well all weekend. This was also rounded out with a party on Saturday night.
Overall, a good event. Look forward to next year's event. I hope to submit a proposal for a talk as well.
20 Books Cybersecurity Professionals Should Read Now
At the recent RSA Conference, Rick Howard, CSO for Palo Alto Networks, gave a popular talk where he gave a recommended list of works he felt cybersecurity professionals should read.
Some are technical, some fiction, and others non-fiction for the general reader.
I have read several, a few I have on my "to read" list, and a few I wasn't aware of. But with that in mind, I plan on reading and reviewing these works over the next few months as possible.
The List? Here it is in alphabetical order.
For those wanting to obtain them:
Some are technical, some fiction, and others non-fiction for the general reader.
I have read several, a few I have on my "to read" list, and a few I wasn't aware of. But with that in mind, I plan on reading and reviewing these works over the next few months as possible.
The List? Here it is in alphabetical order.
- The Blue Nowhere, Jeffery Deaver (2001)
- Breakpoint, Richard A. Clarke (2007)
- The CERT Guide to Insider Threats: How to Prevent, Detect, and Respond to Information Technology Crimes (Theft, Sabotage, Fraud), Dawn M. Cappelli, Andrew P. Moore, and Randall F. Trzeciak (2012)
- Confront and Conceal: Obama’s Secret Wars and Surprising Use of American Power, David Sanger (2013)
- Cryptonomicon, Neal Stephenson (1999)
- The Cuckoo’s Egg: Tracking a Spy Through the Maze of Computer Espionage, Clifford Stoll (1989)
- Cyber War: The Next Threat to National Security and What to Do about It, Richard Clarke and Robert Knake (2010)
- Daemon (2006) and Freedom™ (2010), Daniel Suarez
- Fatal System Error: The Hunt for the New Crime Lords Who Are Bringing Down the Internet, Joseph Menn (2010)
- The Girl with the Dragon Tattoo, Stieg Larssen (2011)
- Kingpin: How One Hacker Took Over the Billion-Dollar Cybercrime Underground, Kevin Poulsen (2011)
- Neuromancer, William Gibson (1986)
- Reamde, Neil Stephenson (2011)
- Security Metrics: Replacing Fear, Uncertainty, and Doubt, Andrew Jacquith (2007)
- Snow Crash, Neal Stephenson (1992)
- We Are Anonymous: Inside the Hacker World of LulzSec, Anonymous and the Global Cyber Insurgency, Parmy Olson (2012)
- Worm: The First Digital World War, Mark Bowden (2011)
- Zero Day (2011) and Trojan Horse (2012), Mark Russinovich
For those wanting to obtain them:
Subscribe to:
Posts (Atom)